3D Biometrics Market Overview
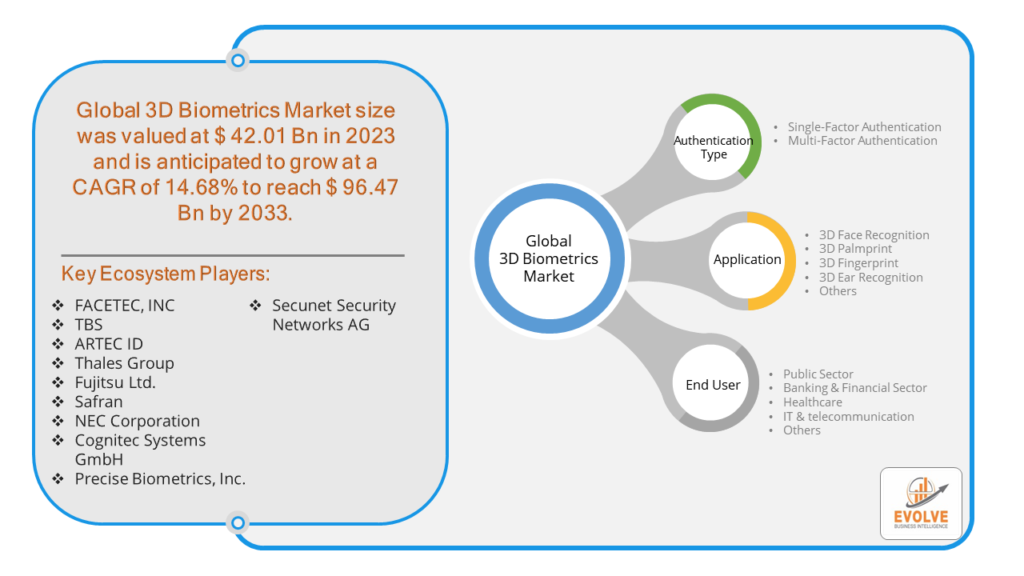
The 3D Biometrics Market Size is expected to reach USD 96.47 Billion by 2033. The 3D Biometrics industry size accounted for USD 42.01 Billion in 2023 and is expected to expand at a compound annual growth rate (CAGR) of 14.68% from 2023 to 2033. The 3D biometrics market encompasses technologies that authenticate or identify individuals based on their unique physical features in three dimensions, including facial recognition, iris recognition, and fingerprint scanning. This market is driven by increasing security concerns in various sectors such as banking, healthcare, and government, leading to a growing demand for accurate and reliable identification systems. Advancements in 3D imaging technologies, coupled with the integration of artificial intelligence and machine learning algorithms, are enhancing the accuracy and efficiency of biometric systems. Additionally, the proliferation of smartphones and IoT devices is further fueling the adoption of 3D biometrics for user authentication and access control. With ongoing research and development, the 3D biometrics market is poised for substantial growth in the coming years.
Global 3D Biometrics Market Synopsis
The 3D Biometrics market experienced a positive impact due to the COVID-19 pandemic. The COVID-19 pandemic has accelerated the adoption of 3D biometrics as contactless authentication solutions gained prominence to minimize physical contact and curb virus transmission. With the increased emphasis on health and safety measures, industries such as healthcare, banking, and transportation are deploying 3D biometric systems for secure and hygienic access control.
Global 3D Biometrics Market Dynamics
The major factors that have impacted the growth of 3D Biometrics are as follows:
Drivers:
⮚ Advancements in Technology
Continuous advancements in 3D imaging technology, such as depth-sensing cameras and structured light systems, have significantly improved the accuracy and reliability of biometric systems. This has expanded the potential applications of 3D biometrics beyond traditional fingerprint and facial recognition to include iris recognition, palm vein recognition, and even gait analysis.
Restraint:
- Privacy Concerns
Biometric data, especially 3D facial scans or iris patterns, is highly sensitive and raises significant privacy concerns. Consumers and regulatory bodies are increasingly scrutinizing how biometric data is collected, stored, and used. Striking a balance between security and privacy while complying with regulations such as GDPR can be challenging for organizations, potentially slowing down the adoption of 3D biometric systems.
Opportunity:
⮚ Retail and Hospitality
The retail and hospitality sectors are adopting 3D biometrics to personalize the customer experience, improve security, and streamline operations. Biometric technologies, such as facial recognition and palm vein recognition, enable retailers to offer tailored shopping experiences, enhance loyalty programs, and prevent theft or unauthorized access to restricted areas.
3D Biometrics Market Segment Overview
By Application
Based on the Application, the market is segmented based on 3D Face Recognition, 3D Palmprint, 3D Fingerprint, 3D Ear Recognition, and Others. Its widespread adoption across various industries, including banking, healthcare, and government, is driven by the technology’s ability to provide seamless and secure authentication in both physical and digital environments. As organizations prioritize enhanced security measures and user-friendly experiences, 3D Face Recognition stands out as the go-to solution for robust identity authentication.
By Authentication Type
 Based on the Authentication Type, the market has been divided into Single-Factor Authentication and Multi-Factor Authentication. By combining multiple layers of verification, such as facial recognition, fingerprint scanning, and iris detection, MFA offers a robust defense against unauthorized access and identity breaches. Its adoption is fueled by the growing awareness of the limitations of single-factor authentication methods, driving organizations to implement more sophisticated and resilient security protocols to safeguard sensitive data and assets.
Based on the Authentication Type, the market has been divided into Single-Factor Authentication and Multi-Factor Authentication. By combining multiple layers of verification, such as facial recognition, fingerprint scanning, and iris detection, MFA offers a robust defense against unauthorized access and identity breaches. Its adoption is fueled by the growing awareness of the limitations of single-factor authentication methods, driving organizations to implement more sophisticated and resilient security protocols to safeguard sensitive data and assets.
By End User
Based on End User, the market has been divided into Public Sector, Banking & Financial Sector, Healthcare, IT & telecommunication, and Others. In the 3D biometrics market, the banking and financial sector emerges as a dominant force, leveraging cutting-edge technology to enhance security measures and protect sensitive financial data. With stringent regulatory requirements and a growing focus on fraud prevention, financial institutions are increasingly adopting 3D biometric solutions to safeguard transactions and authenticate users with unparalleled accuracy and reliability.
Global 3D Biometrics Market Regional Analysis
Based on region, the market has been divided into North America, Europe, Asia-Pacific, the Middle East & Africa, and Latin America. The area of North America is anticipated to dominate the market for the usage of 3D Biometrics, followed by those in Asia-Pacific and Europe.
3D Biometrics North America Market
North America dominates the 3D Biometrics market due to several factors. North America holds the largest market share for 3D biometrics market due to increase investment in safety and security events. North America showed a great economic strength in 2018, holding a share of approximately 42% in 3D biometrics market. Approximately 34 percent of the share is contributed by the US and Canada. Asia Pacific is expected to grow at a highest CAGR during the forecast period.
3D Biometrics Asia Pacific Market
The Asia-Pacific region has been witnessing remarkable growth in recent years. In the Asia-Pacific region, the 3D biometrics market is experiencing robust growth driven by increasing adoption across diverse sectors such as banking, government, and healthcare. Rapid urbanization, digital transformation initiatives, and rising security concerns are fueling the demand for advanced biometric solutions in countries like China, India, and Japan. Government mandates for stricter identity verification coupled with the proliferation of smartphones and IoT devices are further driving market expansion.
Competitive Landscape
The competitive landscape includes key players (tier 1, tier 2, and local) having a presence across the globe. Companies such as FACETEC, INC, TBS, ARTEC ID, Thales Group, and Fujitsu Ltd. are some of the leading players in the global 3D Biometrics Industry. These players have adopted partnership, acquisition, expansion, and new product development, among others as their key strategies.
Key Market Players:
- FACETEC, INC
- TBS
- ARTEC ID
- Thales Group
- Fujitsu Ltd.
- Safran
- NEC Corporation
- Cognitec Systems GmbH
- Precise Biometrics, Inc.
- Secunet Security Networks AG
Key development:
In September 2022, Cognitec Systems GmbH, a leading player in the 3D biometrics market, unveiled a groundbreaking advancement in facial recognition technology. Their latest development showcased enhanced accuracy and efficiency in facial recognition algorithms, setting new standards for identity authentication and access control in various industries worldwide. This innovation reinforced Cognitec’s position as an industry pioneer and fueled its continued growth and prominence in the dynamic field of 3D biometrics.
Scope of the Report
Global 3D Biometrics Market, by Application
- 3D Face Recognition
- 3D Palmprint
- 3D Fingerprint
- 3D Ear Recognition
- Others
Global 3D Biometrics Market, by Authentication Type
- Single-Factor Authentication
- Multi-Factor Authentication
Global 3D Biometrics Market, by End User
- Public Sector
- Banking & Financial Sector
- Healthcare
- IT & telecommunication
- Others
Global 3D Biometrics Market, by Region
- North America
- US
- Canada
- Mexico
- Europe
- UK
- Germany
- France
- Italy
- Spain
- Benelux
- Nordic
- Rest of Europe
- Asia Pacific
- China
- Japan
- South Korea
- Indonesia
- Austalia
- Malaysia
- India
- Rest of Asia Pacific
- South America
- Brazil
- Argentina
- Rest of South America
- Middle East & Africa
- Saudi Arabia
- UAE
- Egypt
- South Africa
- Rest of Middle East & Africa
| Parameters | Indicators |
|---|---|
| Market Size | 2033: $96.47 Billion |
| CAGR | 14.68% CAGR (2023-2033) |
| Base year | 2022 |
| Forecast Period | 2023-2033 |
| Historical Data | 2021 |
| Report Coverage | Revenue Forecast, Competitive Landscape, Growth Factors, and Trends |
| Key Segmentations | Application ,Authentication Type, End User |
| Geographies Covered | North America, Europe, Asia-Pacific, Latin America, Middle East, Africa |
| Key Vendors | FACETEC, INC, TBS, ARTEC ID, Thales Group, Fujitsu Ltd., Safran, NEC Corporation, Cognitec Systems GmbH, Precise Biometrics, Inc., Secunet Security Networks AG |
| Key Market Opportunities | • Government and Defense • Banking and Finance |
| Key Market Drivers | • Privacy Concerns • Accuracy and Reliability |
REPORT CONTENT BRIEF:
- High-level analysis of the current and future 3D Biometrics Industry trends and opportunities
- Detailed analysis of current market drivers, restraining factors, and opportunities analysis in the future
- Historical market size for the year 2021, and forecast from 2023 to 2033
- 3D Biometrics market share analysis for each segment
- Competitor analysis with a comprehensive insight into its product segment, financial strength, and strategies adopted.
- Identifies key strategies adopted by the key players including new product development, mergers and acquisitions, joint ventures, collaborations, and partnerships.
- To identify and understand the various factors involved in the global 3D Biometrics market affected by the pandemic
- To provide year-on-year growth from 2022 to 2033
- To provide short-term, long-term, and overall CAGR comparison from 2022 to 2033.
- Provide Total Addressable Market (TAM) for the Global 3D Biometrics Market.